AWS EKS Monolith Setup
This guide walks you through deploying ThingsBoard CE in monolith mode on AWS EKS. We use Amazon RDS for managed PostgreSQL.
The advantage of monolith deployment via K8S compared to Docker Compose is that in case of an AWS instance outage, K8S will restart the service on another instance.
Prerequisites
Section titled “Prerequisites”Install and configure tools
Section titled “Install and configure tools”Install kubectl, eksctl, and AWS CLI.
Configure your AWS credentials. To get Access and Secret keys, follow this guide. The default region should be the ID of the region where you want to deploy the cluster.
aws configureStep 1. Clone ThingsBoard CE K8S scripts repository
Section titled “Step 1. Clone ThingsBoard CE K8S scripts repository”git clone -b release-4.3 https://github.com/thingsboard/thingsboard-ce-k8s.gitcd thingsboard-ce-k8s/aws/monolithStep 2. Configure and create EKS cluster
Section titled “Step 2. Configure and create EKS cluster”In the cluster.yml file you can find the suggested cluster configuration. Key fields you can change:
| Field | Default | Description |
|---|---|---|
region | us-east-1 | AWS region for the cluster |
availabilityZones | [us-east-1a, us-east-1b, us-east-1c] | Region availability zones |
instanceType | m5.xlarge | EC2 instance type for nodes |
Create the cluster:
eksctl create cluster -f cluster.ymlStep 3. Create AWS load-balancer controller
Section titled “Step 3. Create AWS load-balancer controller”Once the cluster is ready, create the AWS load-balancer controller by following this guide.
The cluster provisioning scripts create several load balancers:
| Load Balancer | Type | Purpose |
|---|---|---|
tb-http-loadbalancer | ALB | Web UI, REST API, HTTP transport |
tb-mqtt-loadbalancer | NLB | MQTT transport |
tb-coap-loadbalancer | NLB | CoAP transport |
tb-edge-loadbalancer | NLB | Edge instances connectivity |
Step 4. Provision databases
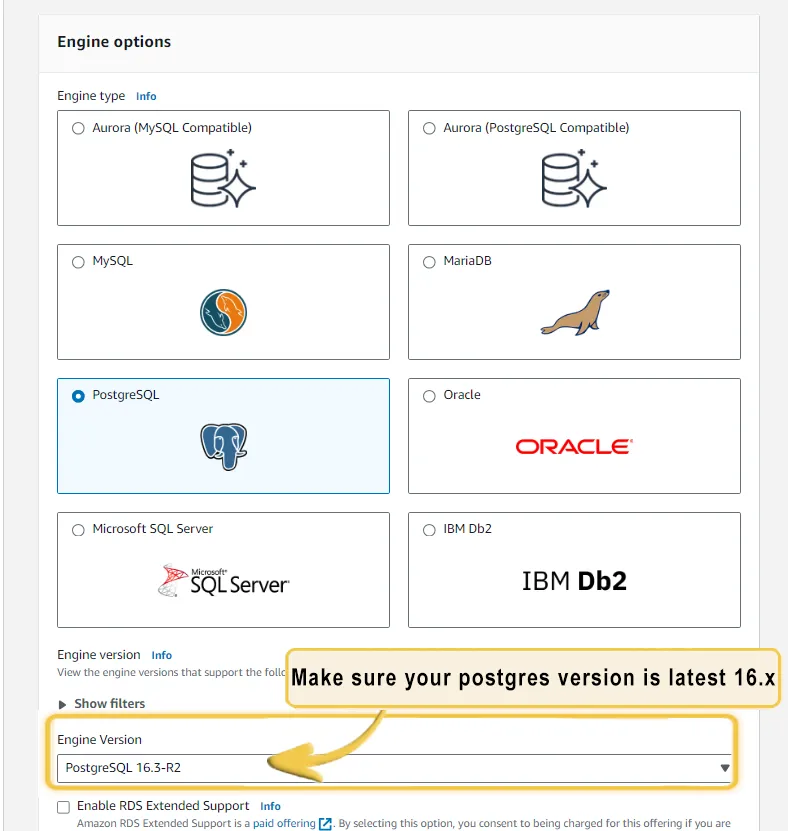
Section titled “Step 4. Provision databases”4.1 Amazon PostgreSQL DB configuration
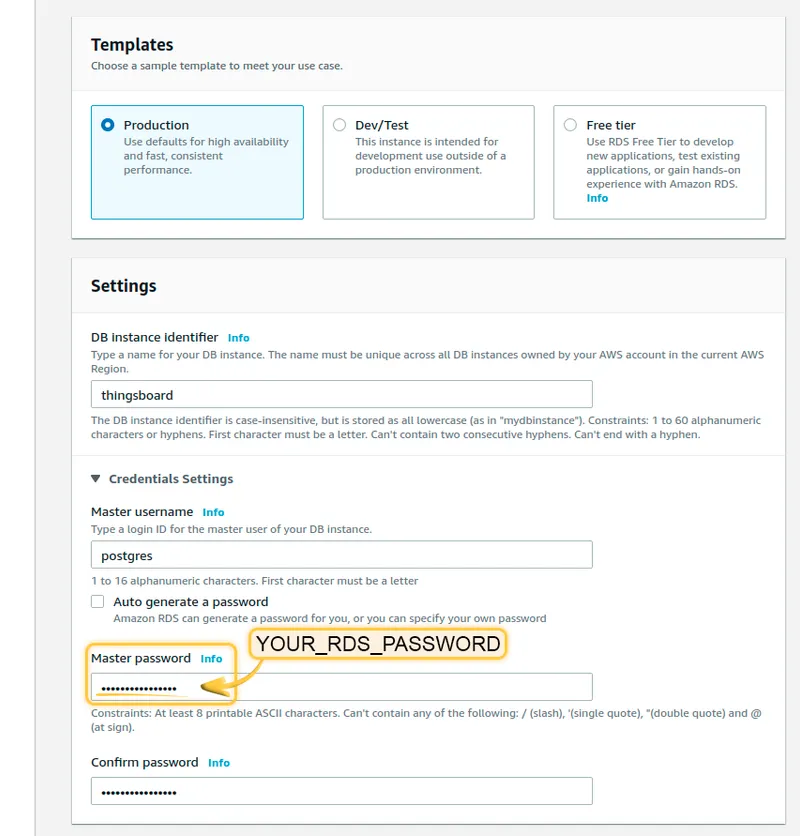
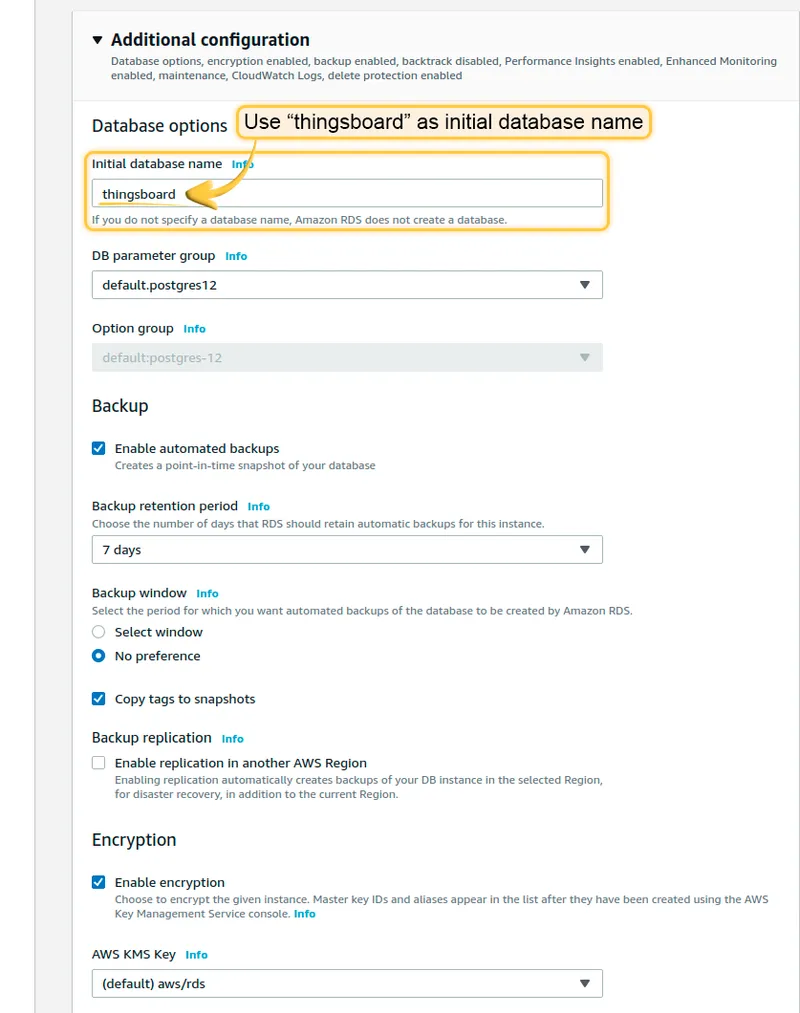
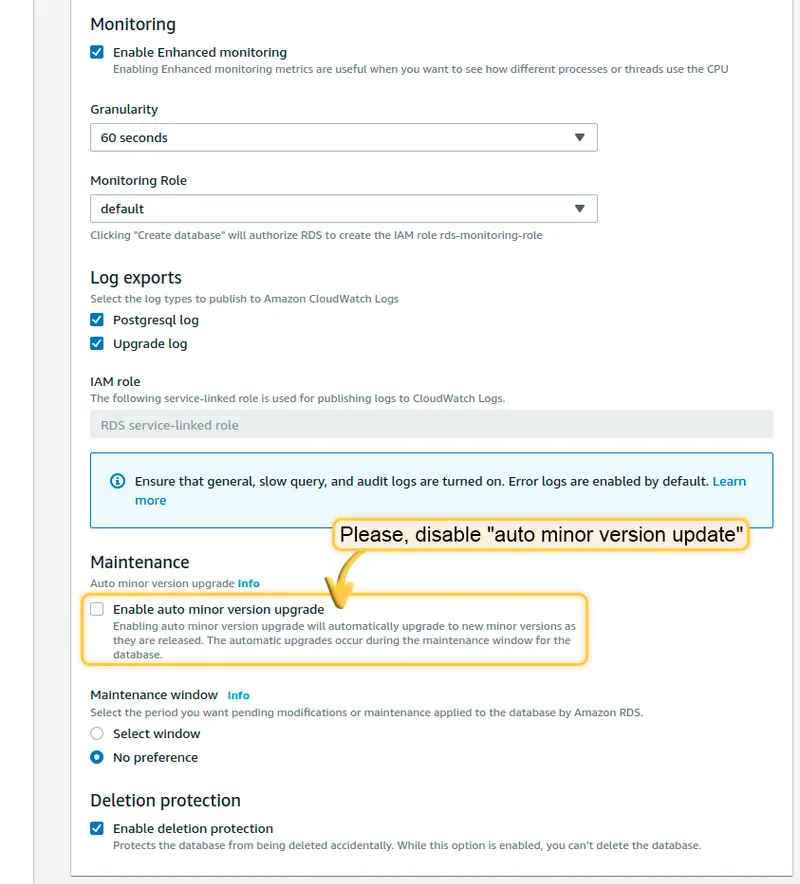
Section titled “4.1 Amazon PostgreSQL DB configuration”Set up PostgreSQL on Amazon RDS. ThingsBoard uses it as the main database for devices, dashboards, rule chains, and device telemetry. Follow this guide, but take into account the following requirements:
- Keep your PostgreSQL password in a safe place. We will refer to it later as YOUR_RDS_PASSWORD.
- Make sure your PostgreSQL version is latest 16.x.
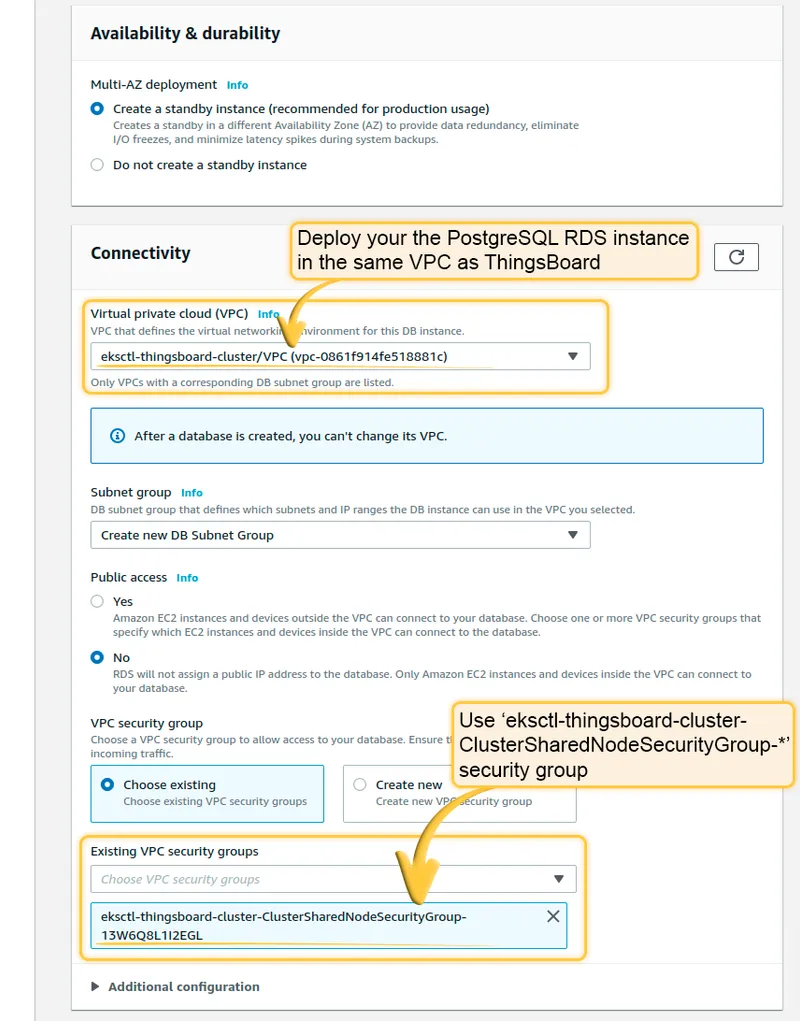
- Make sure your PostgreSQL RDS instance is accessible from the ThingsBoard cluster. The easiest way is to deploy the RDS instance in the same VPC and use the
eksctl-thingsboard-cluster-ClusterSharedNodeSecurityGroup-*security group. - Make sure you use “thingsboard” as the initial database name. If you do not specify a database name, Amazon RDS does not create one.
Recommendations:
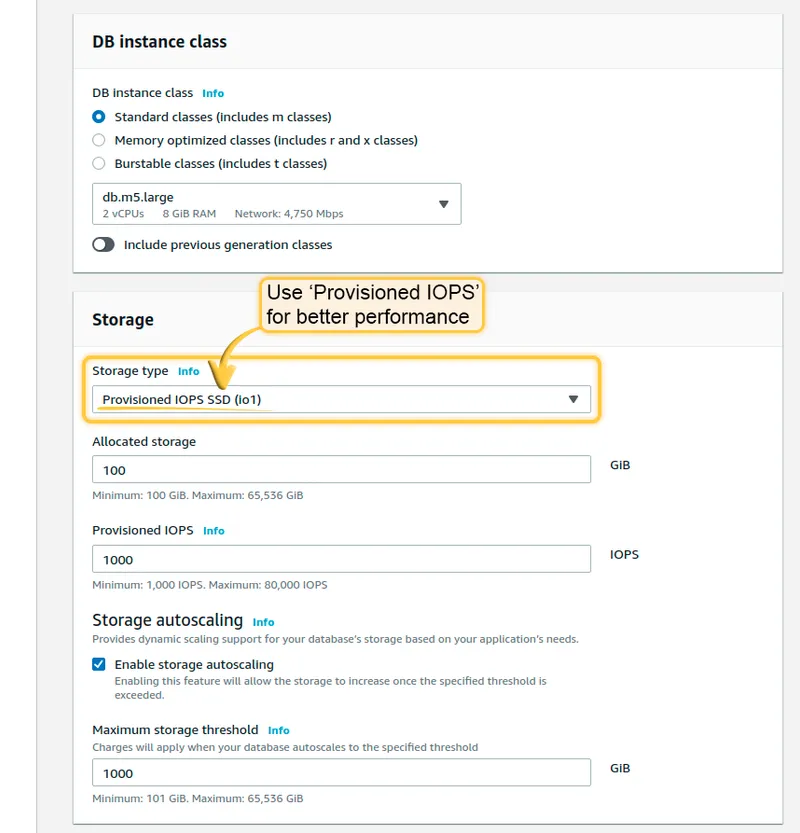
- Use Production template for high availability.
- Use Provisioned IOPS for better performance.
- Consider creating a custom parameters group for your RDS instance.
- Consider deploying the RDS instance into private subnets.
Once the database switches to the Available state, navigate to Connectivity and Security and copy the endpoint value. We will refer to it as YOUR_RDS_ENDPOINT_URL.
Edit tb-node-db-configmap.yml and replace YOUR_RDS_ENDPOINT_URL and YOUR_RDS_PASSWORD.
4.2 Cassandra (optional)
Section titled “4.2 Cassandra (optional)”Using Cassandra is optional. We recommend it if you plan to insert more than 5K data points per second or want to optimize storage space.
Provision additional node groups
Section titled “Provision additional node groups”Create 3 separate node pools with 1 node per zone. At least 4 vCPUs and 16 GB of RAM is recommended.
eksctl create nodegroup --config-file=<path> --include='cassandra-*'Deploy Cassandra stateful set
Section titled “Deploy Cassandra stateful set”kubectl apply -f tb-namespace.ymlkubectl config set-context $(kubectl config current-context) --namespace=thingsboardkubectl apply -f receipts/cassandra.ymlUpdate DB settings
Section titled “Update DB settings”Don’t forget to replace YOUR_AWS_REGION with the name of your AWS region.
echo " DATABASE_TS_TYPE: cassandra" >> tb-node-db-configmap.ymlecho " CASSANDRA_URL: cassandra:9042" >> tb-node-db-configmap.ymlecho " CASSANDRA_LOCAL_DATACENTER: YOUR_AWS_REGION" >> tb-node-db-configmap.ymlCreate keyspace
Section titled “Create keyspace”kubectl exec -it cassandra-0 -- bash -c "cqlsh -e \ \"CREATE KEYSPACE IF NOT EXISTS thingsboard \ WITH replication = { \ 'class' : 'NetworkTopologyStrategy', \ 'us-east' : '3' \ };\""Step 5. Installation
Section titled “Step 5. Installation”Execute the following command to run the initial setup of the database:
./k8s-install-tb.sh --loadDemoWhere --loadDemo is an optional argument to load additional demo data.
After this command finishes you should see:
Installation finished successfully!Step 6. Starting
Section titled “Step 6. Starting”./k8s-deploy-resources.shAfter a few minutes, call kubectl get pods. If everything went fine, you should see tb-node-0 pod in the READY state.
Step 7. Configure load balancers
Section titled “Step 7. Configure load balancers”7.1 Configure HTTP(S) load balancer
Section titled “7.1 Configure HTTP(S) load balancer”You have 2 options:
- HTTP — recommended for development.
- HTTPS — recommended for production. Acts as an SSL termination point.
HTTP load balancer
Section titled “HTTP load balancer”kubectl apply -f receipts/http-load-balancer.ymlCheck the status:
kubectl get ingressUse the address to access the HTTP web UI (port 80) and connect devices via HTTP API.
Default credentials:
- System Administrator: sysadmin@thingsboard.org / sysadmin
- Tenant Administrator: tenant@thingsboard.org / tenant (if demo data loaded)
- Customer User: customer@thingsboard.org / customer (if demo data loaded)
HTTPS load balancer
Section titled “HTTPS load balancer”Use AWS Certificate Manager to create or import an SSL certificate.
nano receipts/https-load-balancer.ymlReplace YOUR_HTTPS_CERTIFICATE_ARN with your certificate ARN, then deploy:
kubectl apply -f receipts/https-load-balancer.yml7.2 Configure MQTT load balancer (optional)
Section titled “7.2 Configure MQTT load balancer (optional)”kubectl apply -f receipts/mqtt-load-balancer.ymlThe load balancer forwards all TCP traffic for ports 1883 and 8883.
One-way TLS
Section titled “One-way TLS”Make the AWS NLB act as a TLS termination point.
nano receipts/mqtts-load-balancer.ymlReplace YOUR_MQTTS_CERTIFICATE_ARN, then deploy:
kubectl apply -f receipts/mqtts-load-balancer.ymlTwo-way TLS
Section titled “Two-way TLS”Follow the MQTT over SSL guide to create a .pem file.
kubectl create configmap tb-mqtts-config \ --from-file=server.pem=YOUR_PEM_FILENAME \ --from-file=mqttserver_key.pem=YOUR_PEM_KEY_FILENAME \ -o yaml --dry-run=client | kubectl apply -f -Uncomment the MQTTS sections in tb-node.yml, then apply:
kubectl apply -f tb-node.ymlkubectl apply -f receipts/mqtt-load-balancer.yml7.3 Configure UDP load balancer (optional)
Section titled “7.3 Configure UDP load balancer (optional)”kubectl apply -f receipts/udp-load-balancer.ymlThe load balancer forwards UDP traffic for ports 5683–5688 (CoAP and LwM2M protocols).
7.4 Configure Edge load balancer (optional)
Section titled “7.4 Configure Edge load balancer (optional)”kubectl apply -f receipts/edge-load-balancer.ymlThe load balancer forwards all TCP traffic on port 7070. Use the external IP as CLOUD_RPC_HOST in Edge connection parameters.
Step 8. Validate the setup
Section titled “Step 8. Validate the setup”Validate Web UI access
Section titled “Validate Web UI access”kubectl get ingressUse the address to open the ThingsBoard web interface.
Validate MQTT/CoAP access
Section titled “Validate MQTT/CoAP access”kubectl get serviceUse the EXTERNAL-IP of tb-mqtt-loadbalancer-external or tb-coap-loadbalancer-external to connect.
Troubleshooting
Section titled “Troubleshooting”kubectl logs -f tb-node-0See the kubectl Cheat Sheet for more details.
Upgrading
Section titled “Upgrading”Merge your local changes with the latest release branch from the repo you cloned in Step 1.
If a database upgrade is needed:
./k8s-upgrade-tb.sh --fromVersion=[FROM_VERSION]Where FROM_VERSION is the starting version. See Upgrade Instructions for valid fromVersion values. You must upgrade versions one by one.
Once completed, re-deploy resources:
./k8s-deploy-resources.shCluster deletion
Section titled “Cluster deletion”./k8s-delete-resources.sh./k8s-delete-all.sheksctl delete cluster -r us-east-1 -n thingsboard -w